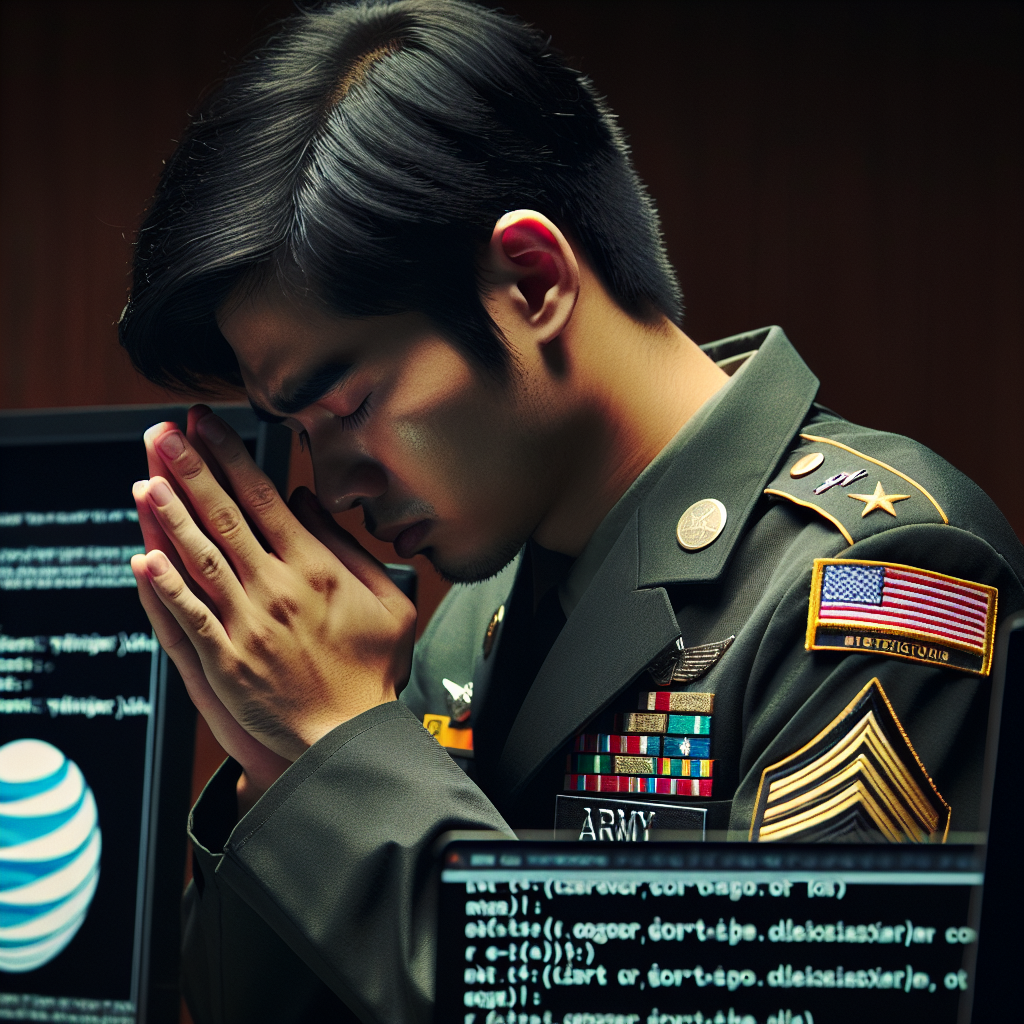
US Army Soldier Pleads Guilty to AT&T and Verizon Hacks: A Deep Dive into Cybersecurity Challenges
In a shocking turn of events, an American soldier stands at the crossroads of two critical national concerns: cybercrime and national security. The recent headlines announcing a US Army soldier pleading guilty to hacking AT&T and Verizon have raised alarms about digital breaches and their wide-ranging impacts. This incident underlines vulnerabilities not just within two of the US’s largest telecommunications companies, but also within the military ranks tasked with protecting the nation.
Cybersecurity is a constantly evolving field with numerous challenges and intricacies. As this case unfolds, it serves as a wake-up call on multiple levels. In this comprehensive article, we’ll explore the finer details of this case, its implications, and the broader cybersecurity landscape that affects us all.
The Case Overview
Who is Involved?
The central figure in this case is a US Army soldier whose identity has been protected thus far, pending further legal procedures. Allegedly, this soldier leveraged insider knowledge and unauthorized access to infiltrate the internal systems of AT&T and Verizon, two of the biggest telecommunications firms in the United States.
What Happened?
Reports indicate that the hacks were driven by the motive of financial gain. It’s been revealed that the soldier accessed sensitive customer data, presumably to sell the information on the dark web. Utilizing a range of sophisticated software tools and techniques, these breaches remained undetected for a significant period, allowing access to potentially thousands of customer records.
Implications of the Hacks
Impact on Consumers
When data breaches occur, consumers feel the immediate impact. Here’s how customers of AT&T and Verizon could be affected:
- Personal Data Exposure: Personal information such as names, addresses, Social Security numbers, phone numbers, and more may have been compromised.
- Financial Risk: With access to personal data, hackers could attempt identity theft or financial fraud, making unauthorized transactions or opening lines of credit.
Corporate Consequences
For AT&T and Verizon, the hacks bring numerous concerns:
- Legal and Financial Repercussions: These breaches could lead to substantial fines and legal actions as both companies may be accused of failing to protect customer data effectively.
- Reputational Damage: Trust is paramount in the digital age. Breaches can deter customers, leading to a loss in market share and revenue.
Military Concerns
The involvement of a soldier in such a cybercrime is unprecedented and raises additional questions:
- **Security Clearance Risks:** The soldier’s actions highlight potential vulnerabilities in military security systems, potentially compromising national security.
- **Internal Scrutiny:** This case could trigger a comprehensive audit of cybersecurity protocols, including personnel vetting processes, to prevent future incidents.
Understanding Cybercrime Within Telecommunication
Why Target Telecommunication Companies?
Telecommunication companies are tempting targets for hackers due to:
- Massive Customer Base: More customers mean more data to exploit.
- Hub of Communications: These companies facilitate global communication networks, affecting numerous sectors.
- Technological Infrastructure: Gaining access can potentially disrupt communications, giving power to initiators of the breach.
Methods Employed in the Hacks
- Phishing Attacks: Often utilized to gain initial access by tricking employees into revealing login details.
- Social Engineering: Manipulating insiders to provide information unwittingly.
- Exploiting Vulnerabilities: Using zero-day exploits and other vulnerabilities to bypass security measures.
Evolving Cybersecurity Measures
To safeguard against future breaches, the focus on cybersecurity must be relentless.
For Telecommunication Companies
- Comprehensive Security Solutions: Implement multi-layered cybersecurity measures, including firewalls and encryption.
- Regular Security Audits: Constantly monitor and test systems for vulnerabilities.
- Employee Education: Train employees to recognize and respond to phishing and other cyber threats.
For the Military
- Secure Communication Channels: Ensure military communications are encrypted and secure.
- Regular Background Checks: Continually assess personnel’s clearance and integrity.
- Advanced Surveillance of Network Activity: Employ AI-driven monitoring tools to detect unusual activities promptly.
Legal Framework and Future Endeavors
Existing Laws
Both companies and military institutions must adhere to strict data protection laws including:
- The Cybersecurity Information Sharing Act (CISA)
- The Federal Information Security Management Act (FISMA)
- The General Data Protection Regulation (GDPR) for foreign interactions
Future Directions
Law enforcement and legal frameworks must evolve continually to keep pace with cybercriminals.
- Stricter Regulations and Penalties: Implement harsher punishments to deter prospective hackers.
- International Cooperation: Cybercrime often transcends borders, necessitating global collaboration.
Conclusion
The incident involving a US Army soldier pleading guilty to the AT&T and Verizon hacks highlights the intricate and evolving risks associated with cybersecurity. It underscores the substantial responsibility companies, militaries, and regulators have in securing data and maintaining trust. As we adapt to new digital threats, it remains crucial to prioritize cybersecurity at every level to protect sensitive information and safeguard against potential breaches in the future.
In a world where information is power, ensuring its safety is paramount. Stay informed, stay connected, and above all, stay secure.